The act of unlawfully taking a Pokmon from another individual is a significant concern within the Pokmon community and in legal contexts where applicable. This encompasses a range of actions, from simple theft of physical trading cards to more complex instances of illegally accessing and transferring digital Pokmon data. For example, an individual might steal a valuable holographic card from a collector’s binder, or gain unauthorized access to a player’s online account and transfer their Pokmon to another account without permission.
This type of illicit activity undermines the integrity of the Pokmon ecosystem, impacting both collectors and players. For collectors, the loss of valuable cards can result in significant financial repercussions. For players, the theft of their digital Pokmon can be emotionally distressing, as these Pokmon often represent hours of dedication and strategic team-building. Historically, concern over these issues has grown alongside the increasing value and popularity of both physical and digital Pokmon assets, leading to greater awareness of security measures and legal ramifications.
The following sections will explore specific instances, security measures, and potential legal ramifications associated with the unauthorized acquisition of Pokmon assets. It will delve into both the tangible and digital realms, outlining the steps individuals can take to protect their Pokmon and the recourse available should they become victims.
Safeguarding Pokémon Assets
Protecting against the unauthorized acquisition of Pokémon, whether physical cards or digital data, requires diligent adherence to best practices. Implementing the following measures can significantly reduce the risk of falling victim to illicit activity.
Tip 1: Physical Card Security: Secure valuable trading cards in locked, waterproof cases, preferably stored in a secure, climate-controlled environment. Catalog card inventories with photographs and serial numbers (where available) for insurance and recovery purposes.
Tip 2: Digital Account Protection: Employ strong, unique passwords for all Pokémon-related online accounts. Enable two-factor authentication (2FA) wherever possible to add an additional layer of security beyond a simple password.
Tip 3: Beware of Phishing Attempts: Exercise extreme caution when clicking links or opening attachments in emails or messages, especially those requesting personal information or account credentials. Verify the sender’s authenticity before providing any data.
Tip 4: Secure Trading Practices: When engaging in online trades, utilize reputable platforms with established feedback systems. Carefully scrutinize the trading partner’s history and avoid high-value trades with unverified individuals.
Tip 5: Software Security Updates: Maintain up-to-date antivirus and anti-malware software on all devices used to access Pokémon-related online services. Regularly scan systems for potential threats.
Tip 6: Limit Third-Party Apps and Modifications: Avoid installing unofficial applications or game modifications, as these can introduce security vulnerabilities and compromise account integrity. Adhere strictly to the terms of service for all Pokémon-related games and services.
Implementing these security measures significantly reduces vulnerability to the loss of valuable Pokémon assets. Vigilance and proactive security management are crucial for safeguarding both physical and digital collections.
The following sections will discuss specific scenarios and legal recourse available in instances of compromised security and unauthorized acquisition.
1. Card Valuation Fluctuations
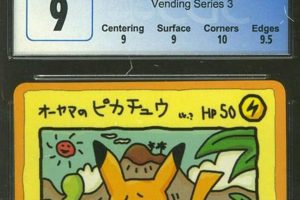
The fluctuations in the valuation of Pokémon trading cards directly correlate with the incentive for theft. As the perceived or actual monetary value of specific cards increases, so does the likelihood of those cards becoming targets of unlawful acquisition.
- Rarity and Demand Amplification
High-value cards are frequently those possessing a combination of rarity and sustained demand. Limited print runs, errors, or unique characteristics can drastically increase desirability among collectors, driving up market prices and, consequently, the temptation for theft. A first edition Charizard, for example, could fetch substantial sums, making it a prime target for illicit activity. This is not limited to vintage cards; contemporary cards with limited availability also experience similar value spikes.
- Market Manipulation Effects
Artificial inflation of card values, whether through coordinated buying strategies or speculative investments, can create a false sense of scarcity and drive prices to unsustainable levels. This artificial inflation can subsequently lead to a surge in theft, as individuals perceive the cards as quick and easy sources of revenue. The perception of guaranteed profit increases the risk of criminal activity.
- Accessibility of Market Information
The widespread availability of market data, through online auction sites and price tracking tools, provides potential perpetrators with readily accessible information regarding the value of specific cards. This data allows them to identify high-value targets and plan accordingly, making theft a more calculated and informed endeavor. The ease with which potential targets can be identified contributes to the problem.
- Reduced Risk Perception
Compared to other forms of theft, stealing Pokémon cards may be perceived as a lower-risk crime, particularly if the victim is not expected to report the theft or if the perpetrator believes the cards can be easily fenced. This perceived reduction in risk, combined with the potential for financial gain, can further incentivize theft, particularly among those seeking quick monetary returns.
These factors demonstrate the intricate connection between market valuations and criminal activity. Fluctuations in card values amplify the potential financial gain from illicit acquisition, thereby increasing the likelihood of card theft. Addressing this issue requires a multi-faceted approach that includes improved security measures, increased community awareness, and diligent monitoring of market trends.
2. Digital Account Breaches
Digital account breaches represent a significant avenue through which unauthorized acquisition of Pokémon assets occurs. The compromised security of online accounts facilitates illicit transfer and manipulation of digital Pokémon data, impacting players and the overall integrity of the game ecosystem.
- Compromised Credentials and Unauthorized Access
The primary means of a digital account breach involves gaining unauthorized access through compromised login credentials. This can occur via phishing scams, where individuals are tricked into revealing their usernames and passwords, or through brute-force attacks that systematically attempt to guess login combinations. Once an attacker gains access, they can transfer Pokémon to their own accounts, trade them for personal gain, or even delete them outright, causing significant distress and loss for the account owner. For example, an individual’s email being compromised leading to access to Pokemon GO and valuable Pokemon being transferred.
- Exploitation of Game Vulnerabilities
Software vulnerabilities within the Pokémon game applications or related platforms can be exploited to gain unauthorized access to player accounts. Hackers may discover and utilize flaws in the game’s code to bypass security measures and manipulate account data. This type of breach can be particularly damaging, as it may affect a large number of accounts simultaneously. A weakness in the authentication process, for example, could be exploited to mass-hijack accounts.
- Malware and Keylogging
Malicious software, such as keyloggers or Remote Access Trojans (RATs), can be installed on a user’s device without their knowledge, recording keystrokes and other sensitive information, including login credentials for Pokémon-related accounts. This information can then be transmitted to attackers, allowing them to gain complete control over the compromised account. Downloading a compromised Pokémon fan game could lead to an account being hacked, as an example.
- Third-Party Application Risks
Using unofficial or third-party applications that interact with Pokémon games or online services introduces security risks. These applications may request access to account information or introduce malware that compromises account security. While some third-party tools may offer legitimate functionality, they often lack the security safeguards of official applications, making them attractive targets for malicious actors. Use of IV checkers and other third-party software have inherent risks.
These varied attack vectors highlight the vulnerability of digital Pokémon assets to account breaches. The consequences of such breaches range from the loss of valuable in-game resources to emotional distress for dedicated players. Protecting against digital account breaches requires vigilance, strong security practices, and awareness of the potential risks associated with interacting with Pokémon-related online services.
3. Counterfeit Product Circulation
The circulation of counterfeit Pokémon products is inextricably linked to illicit asset acquisition. While not direct theft of legitimate items, counterfeit creation and distribution incentivize and enable fraudulent activities. Counterfeits undermine market value, fueling theft of genuine articles by diminishing collector confidence and blurring lines between genuine and fake products. For instance, the mass production of fake rare cards creates an environment where buyers are unsure of authenticity, leading them to seek “deals” that may involve stolen merchandise sold as genuine. The availability of counterfeit merchandise diminishes the value and prestige of authentic items, indirectly incentivizing the theft of the real thing as thieves see it as an easy target.
The presence of counterfeit items creates a channel for the illicit trade of stolen authentic products. Sellers of fake cards may mix in genuine stolen cards to add credibility to their offerings, making it harder for buyers to distinguish between legitimate and illegitimate sources. This complex ecosystem, fed by both counterfeit and genuine stolen items, necessitates robust verification and authentication methods. Counterfeit products also defraud consumers, particularly those who are new to the hobby and unaware of the differences between real and fake cards. This fraud can erode trust in the market, leading collectors to seek avenues outside of legitimate channels where stolen cards may circulate.
In summary, counterfeit product circulation is a significant enabler of illicit asset acquisition, not merely a parallel issue. Counterfeit production undermines market stability, reduces collector confidence, and provides a channel for stolen goods to enter the market. Effective countermeasure against theft must address counterfeit product circulation through consumer education, rigorous law enforcement, and the development of robust authentication technologies.
4. Unlawful Data Transfer
Unlawful data transfer constitutes a core element of digital instances, where the unauthorized movement of Pokémon game data and account information directly enables the act of theft. This transfer can manifest through several methods, all resulting in the illegitimate acquisition of digital Pokémon assets. The illegal manipulation of game servers, for instance, allows perpetrators to move Pokémon from one account to another without proper authorization. Similarly, exploiting vulnerabilities in trading systems facilitates the transfer of valuable Pokémon to malicious actors. A practical instance is an individual gaining access to another player’s account via phishing, and then transferring the victim’s rare Pokémon to a secondary account under their control. Without the capability to unlawfully move this data, the act of digital Pokémon theft would be significantly curtailed, highlighting the intrinsic link between the two.
The significance of unlawful data transfer extends beyond individual incidents, affecting the overall integrity of the Pokémon gaming ecosystem. Each successful data breach and illicit transfer undermines the trust players place in the security of their accounts and the fairness of the game. Consider the impact of widespread reports of “cloned” Pokémon appearing in online battles; this stems from unauthorized duplication and transfer of Pokémon data, creating an uneven playing field and diminishing the value of legitimate achievements. Game developers address this challenge by implementing increasingly sophisticated encryption methods and server-side validations to detect and prevent unauthorized data manipulation. The ongoing conflict between malicious actors and game developers exemplifies the constant effort to secure Pokémon data against illicit transfer.
In summary, unlawful data transfer serves as the primary mechanism by which digital Pokémon theft is executed. Its prevention is critical to maintaining the integrity of the game environment and ensuring the security of player assets. The challenge lies in continuously adapting security measures to counter evolving techniques of unauthorized data manipulation. Successfully mitigating unlawful data transfer is essential for the long-term viability and enjoyment of Pokémon games in the digital realm.
5. Trade Scam Tactics
Trade scam tactics represent a significant subset of activities contributing to the overall problem of Pokémon theft, functioning as a deceptive means to illegitimately acquire assets from unsuspecting individuals. These tactics exploit vulnerabilities in trading systems, trust within the community, or lack of awareness among players. The core outcome is the same as direct theft: an individual is deprived of their Pokémon or related assets through fraudulent means. An example is the “bait and switch” tactic, where a player agrees to trade a valuable Pokémon for another, but at the last moment replaces the valuable Pokémon with a less desirable one, hoping the other player won’t notice before confirming the trade. This form of deception allows the perpetrator to acquire a valuable Pokémon under false pretenses, effectively stealing it through trickery.
Understanding the diverse range of trade scam tactics is crucial for preventing losses and protecting oneself from becoming a victim. Common schemes include offering duplicated or counterfeit items in trades, promising future favors that never materialize, or leveraging emotional manipulation to pressure others into unfair trades. A seller advertising a Pokémon for sale and then taking the payment without providing the item, also know as “ghosting”. Recognizing these tactics is the first line of defense. Trading platforms often implement feedback systems and reporting mechanisms to combat scamming, but these rely on users being vigilant and proactive in identifying and reporting suspicious behavior. Educating new players about prevalent scam tactics is thus an essential community responsibility, fostering a safer trading environment and reducing the appeal of such fraudulent activities.
In conclusion, trade scam tactics are a component of illicit asset acquisition, impacting both individual victims and the overall health of the Pokémon trading community. Combating these tactics requires a combination of individual vigilance, platform-level security measures, and community-driven education. By understanding and actively addressing trade scam tactics, participants in the Pokémon ecosystem can mitigate their vulnerability and contribute to a more secure and trustworthy environment, thereby reducing the prevalence of effective theft.
6. Legal Recourse Options
The availability of legal recourse options is directly contingent upon the nature and scope of the incident, and applicable jurisdictional laws. These avenues aim to provide redress to individuals or entities that have suffered loss due to illicit acquisition.
- Civil Litigation
Civil lawsuits offer a pathway for victims to seek compensation for damages incurred through the unauthorized taking of Pokémon property. These damages can encompass the monetary value of stolen cards, the cost of recovering compromised digital accounts, or emotional distress caused by the theft. Successful litigation hinges on proving ownership of the stolen assets and demonstrating a direct link between the defendant’s actions and the plaintiff’s losses. An example would involve a collector suing an individual who stole valuable cards from their residence, seeking compensation for their replacement value.
- Criminal Prosecution
Criminal prosecution involves the state bringing charges against the perpetrator of illicit acquisition. The applicability of criminal law depends on the nature of the illicit taking (theft, fraud, etc.) and the value of the assets stolen. Successful prosecution can result in fines, imprisonment, or both. The involvement of law enforcement is crucial in gathering evidence and building a case against the alleged perpetrator. A case where an individual is arrested and charged with theft for stealing Pokémon cards from a retail store illustrates criminal prosecution.
- Terms of Service Agreements
Terms of Service Agreements (ToS) associated with online Pokémon games and trading platforms often outline specific policies regarding account security, data ownership, and prohibited conduct. Violations of these ToS, such as unauthorized account access or data manipulation, can result in account suspension or termination. While not directly constituting legal recourse, enforcement of ToS by game developers or platform operators can provide a measure of protection against digital asset theft. A game developer banning a player for using unauthorized software to steal Pokémon is an instance of enforcing the ToS agreement.
- Insurance Claims
Insurance policies, such as homeowners or collectibles insurance, may provide coverage for losses resulting from theft or damage to Pokémon assets. The specific coverage terms and conditions vary depending on the policy. Filing an insurance claim requires providing documentation of ownership and the value of the stolen items. A homeowner’s insurance policy covering the loss of Pokémon cards stolen during a burglary demonstrates this type of legal recourse.
These legal recourse options provide avenues for addressing losses stemming from illicit acquisition. The suitability of each option depends on the specific circumstances of the incident, the applicable laws, and the available evidence. Victims are advised to consult with legal counsel to assess their options and pursue the most appropriate course of action.
7. Community Awareness Initiatives
Community awareness initiatives serve as a crucial deterrent against unlawful taking within the Pokémon ecosystem. By educating players and collectors about the methods employed by perpetrators, the value of assets, and preventative security measures, these initiatives reduce the likelihood of successful illicit acquisition. Information dissemination, such as online guides detailing common scam tactics or forums sharing experiences with theft, empowers individuals to recognize and avoid potential threats. A real-world example is organized groups creating public service announcements on social media platforms warning about phishing schemes targeting Pokémon GO accounts. Such efforts directly mitigate the risk of digital theft by increasing user awareness.
These initiatives not only focus on prevention but also foster a collective responsibility for security within the community. Reporting platforms and support networks encourage victims to share their experiences, leading to the identification of repeat offenders and the development of community-driven solutions. For instance, online trading communities that maintain blacklists of known scammers and require verification processes for high-value trades demonstrably reduce fraudulent transactions. This collaborative approach contrasts with individual efforts, creating a stronger defense against sophisticated theft operations and promoting trust among participants. Furthermore, successful awareness campaigns can exert pressure on game developers and trading platforms to implement enhanced security features.
In summary, community awareness initiatives are a vital component in combating unauthorized acquisition within the Pokémon realm. They proactively educate individuals, foster collective responsibility, and indirectly influence security improvements by developers. While challenges remain in reaching all members of the community and adapting to evolving theft methods, the practical significance of these initiatives lies in their demonstrated ability to reduce vulnerability and cultivate a safer environment for all participants. Continuously promoting and supporting such initiatives is fundamental to preserving the integrity of the Pokémon experience.
Frequently Asked Questions Regarding Pokmon Theft
The following questions address common concerns and misunderstandings surrounding the unlawful acquisition of Pokémon assets, encompassing both physical and digital forms. The information provided aims to clarify potential ramifications and preventative measures.
Question 1: What constitutes as an act in Pokmon theft?
It encompasses a range of activities, from physical theft of trading cards to unauthorized access and transfer of digital Pokémon data, effectively depriving an individual of their rightfully obtained assets.
Question 2: Why is Pokmon theft a serious issue?
It undermines the integrity of the Pokémon community, causing financial loss for collectors and emotional distress for players who invest time and effort into acquiring and training their digital Pokémon.
Question 3: What are the primary methods used in Pokmon theft?
Methods include physical break-ins to steal trading cards, phishing scams to acquire login credentials for digital accounts, and exploitation of vulnerabilities in game software to facilitate unauthorized data transfer.
Question 4: What are the potential legal consequences of Pokmon theft?
Depending on the value of the stolen assets and the jurisdiction, perpetrators may face civil lawsuits seeking monetary damages or criminal charges leading to fines and imprisonment.
Question 5: How can individuals protect themselves from Pokmon theft?
Security measures include securing physical card collections in locked cases, using strong and unique passwords for online accounts, enabling two-factor authentication, and exercising caution when clicking links or downloading attachments from unknown sources.
Question 6: What role does the community play in preventing Pokmon theft?
Community awareness initiatives, such as sharing information about common scams and reporting suspicious activity, are crucial in fostering a safer environment and deterring potential offenders.
Understanding the various facets of unlawful acquisition and implementing preventative measures is essential for safeguarding Pokémon assets. Vigilance and proactive security management are key in mitigating the risks.
The subsequent article sections will delve into advanced security strategies and emerging threats within the landscape of illicit acquisition.
Conclusion
This exploration has illuminated the multifaceted nature of “pokemon theif,” extending beyond simple card theft to encompass digital account breaches, data manipulation, and elaborate trade scams. The value, both monetary and emotional, invested in these assets fuels a persistent incentive for illicit acquisition. Securing both physical collections and digital accounts requires vigilance, knowledge of prevalent tactics, and proactive implementation of security measures.
The ongoing effort to combat illicit acquisition demands a collective commitment from individuals, communities, and game developers. By fostering awareness, sharing knowledge, and supporting robust security protocols, the Pokémon community can mitigate the risks and protect the integrity of the ecosystem for all participants. The future of Pokémon collecting and gaming depends, in part, on sustained efforts to deter and prevent “pokemon theif” in all its evolving forms.